How to connect Microsoft Defender for Office 365 to your HighGround account
Sync your Email Filtering data from Microsoft Defender for Office 365
You can integrate your Microsoft Defender for Office 365 account with HighGround to retrieve your Email Filtering data. This data can then be used to drive your Cyber KPI's. In order to synchronise this data to your HighGround account, you will need to connect to Microsoft Defender for Office 365 API by setting up an App Registration with the relevant permissions in your Azure Tenant, and then integrating the tool via the Integrations module.
The following process is reasonably technical, so please have a member of your IT team complete this if you do not have any prior experience with API's.
Please follow the steps below to generate API credentials for Microsoft Defender for Office 365 first, before moving onto our guide on How to Integrate a tool with your HighGround account.
STEP 1: Log in to Azure
Note
You must be a Global Administrator of the Azure Tenant to set up the API.
Login to Azure using a Global Administrator account.
STEP 2: Retrieve your Tenant ID
The integration will require your Tenant ID.
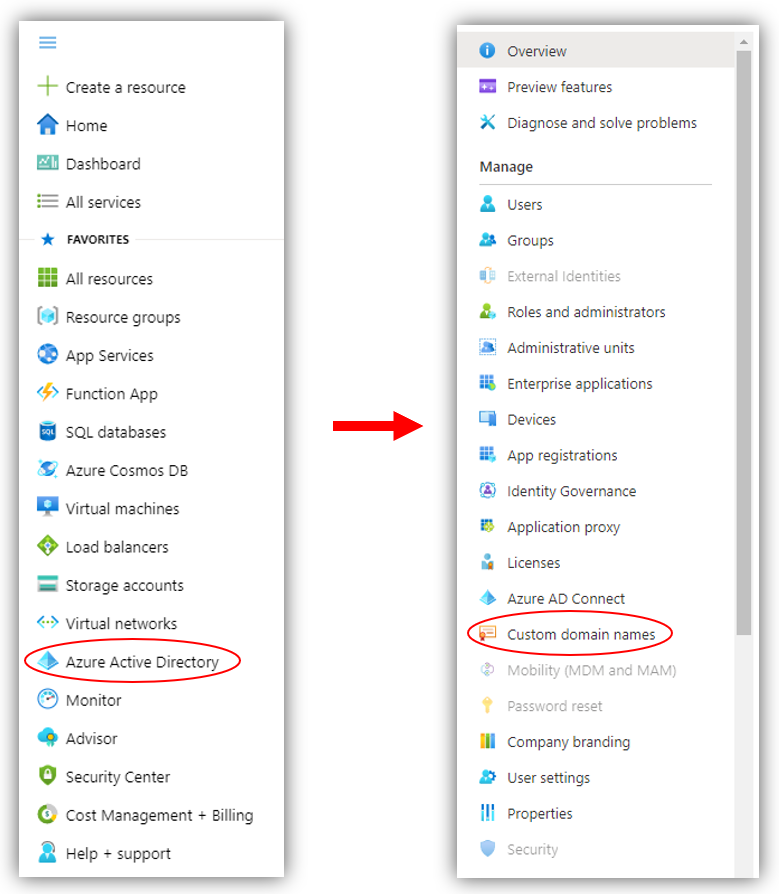
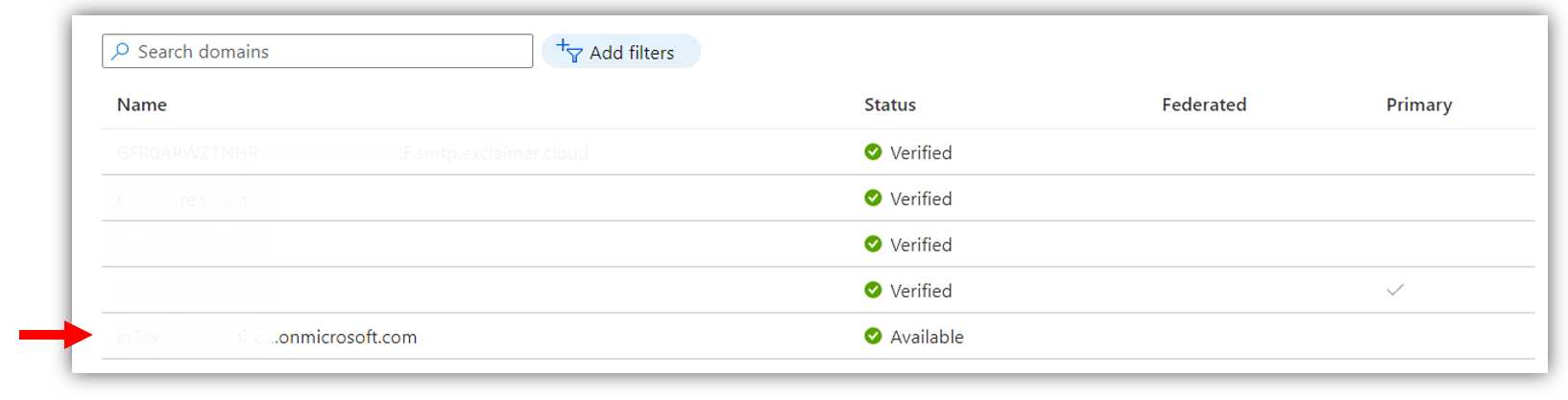
To find your Tenant ID, click on Active Directory from the main left-hand menu, and then navigate to Custom Domain Names:
You should now be able to see a list of your domains (these have been blanked out in the screenshot below).
Your tenant ID is the domain ending with '.onmicrosoft.com'.
Take a note of this as you will need it in the last step of this guide.
STEP 3: Go to App Registrations
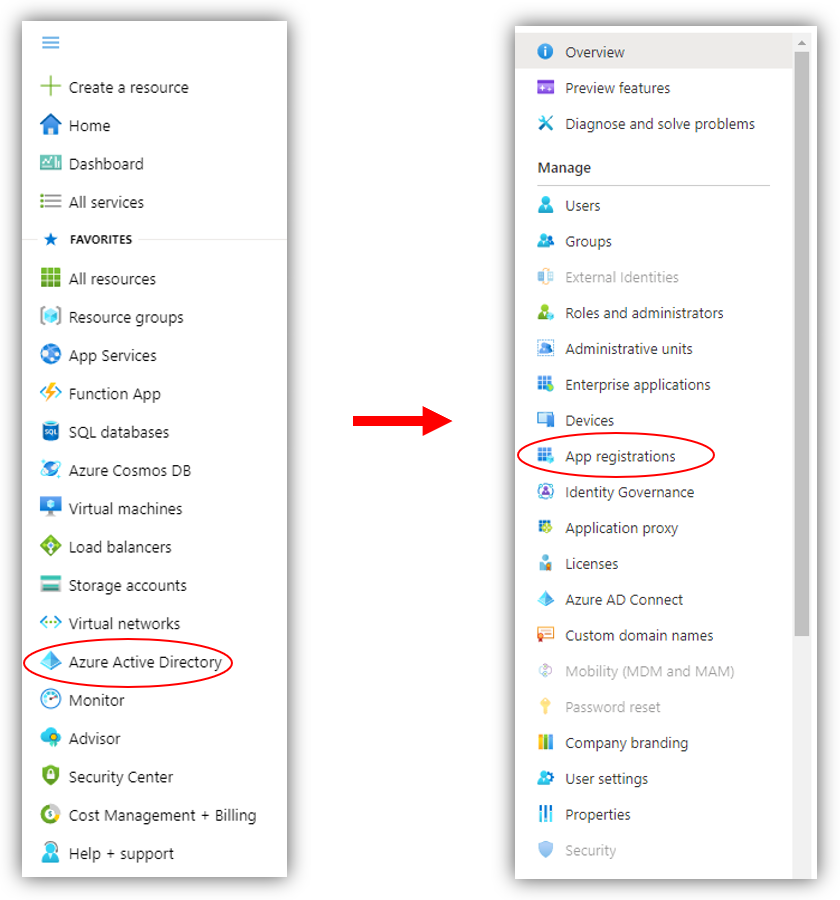
From the main left-hand menu of Azure, click on Azure Active Directory, and from there navigate to App registrations:
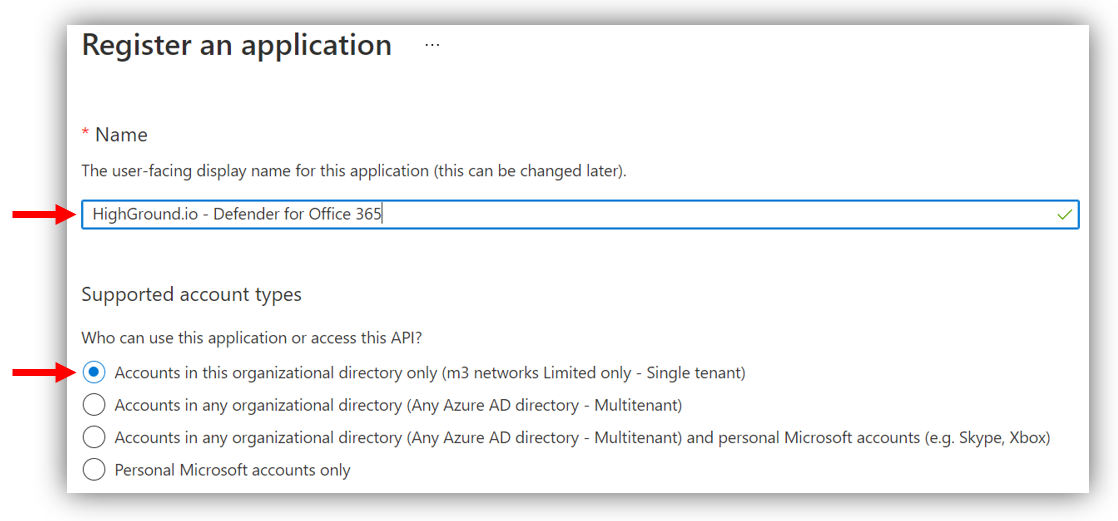
STEP 4: Register Application
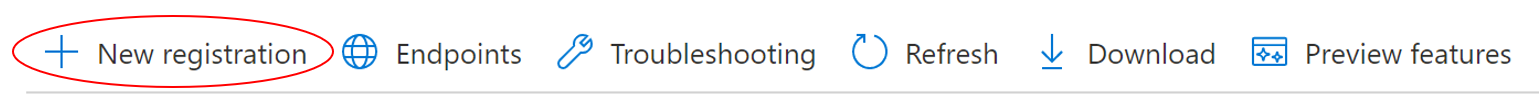
Once in App Registrations, click on the New Registration tab.
You will now see a window where you can add the details of your application.
- Name: HighGround.io - Defender for Office 365
- Supported Account types: ensure the default option 'Accounts in this organizational directory only' is ticked
- Leave the option to add a Redirect URI blank
After adding those details, click the Register button to finish registering your application.
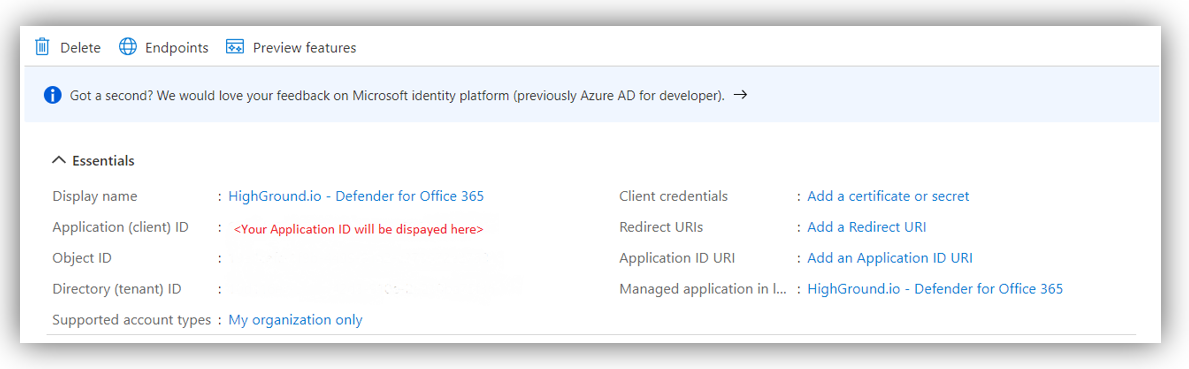
STEP 5: Retrieve your Application ID
Now you have registered the Application, you will be taken to an overview of its details.
In the second row of this list, you will find your Application (client) ID. This ID will be a 32-character string separated by hyphens.
Keep a note of your Application (Client) ID as this will be needed in the final step of this guide.
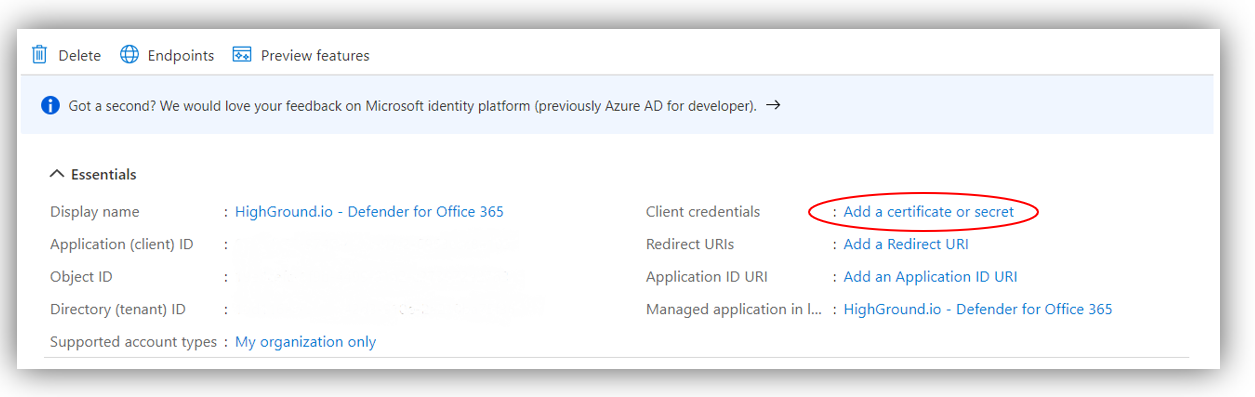
STEP 6: Upload Certificate
Whilst still within the Application overview, click on Add a certificate or secret option next to Client Credentials:
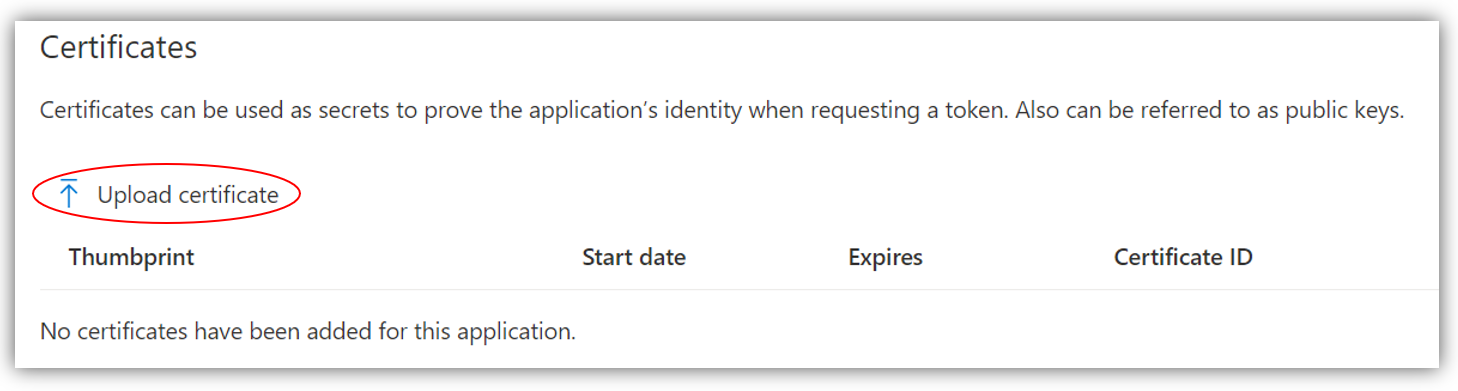
From there, click Upload Certificate:
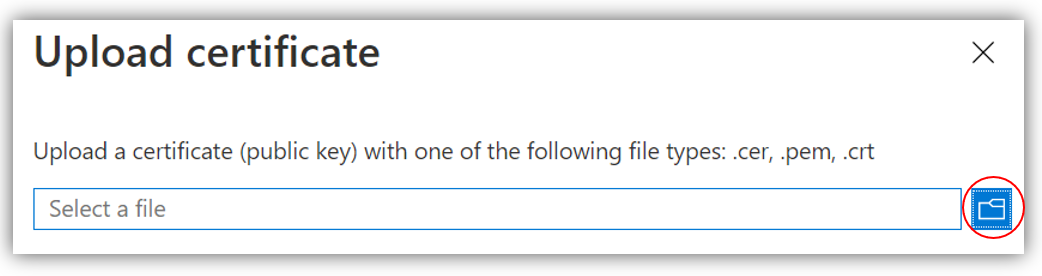
This will open a new window where you can attach your certificate. Please download the required certificate here: o365-def4email-auth.highgroundio.crt
Once you have downloaded the certificate, click the folder icon, and upload the certificate from your files.
Once you have uploaded the certificate, click Add.
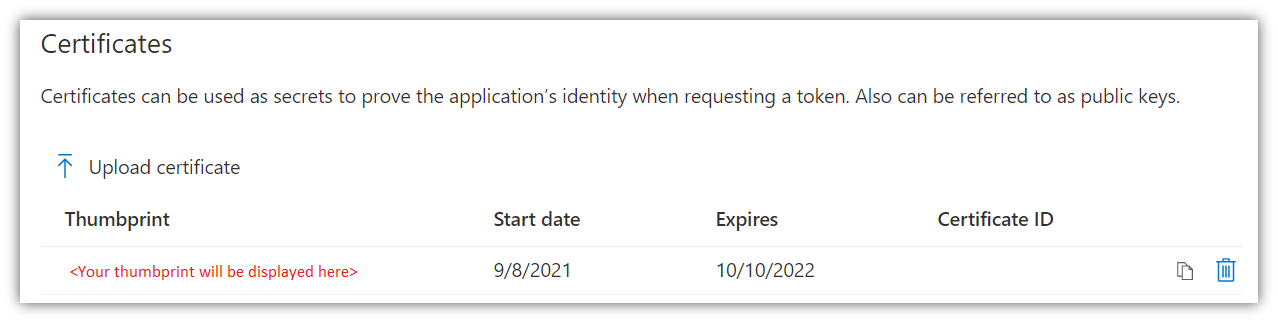
If you have successfully uploaded the certificate, you should now see a Certificate Thumbprint under the Certificates field:
STEP 6: Assign Permissions
You now need need to allocate permissions to the App registration.
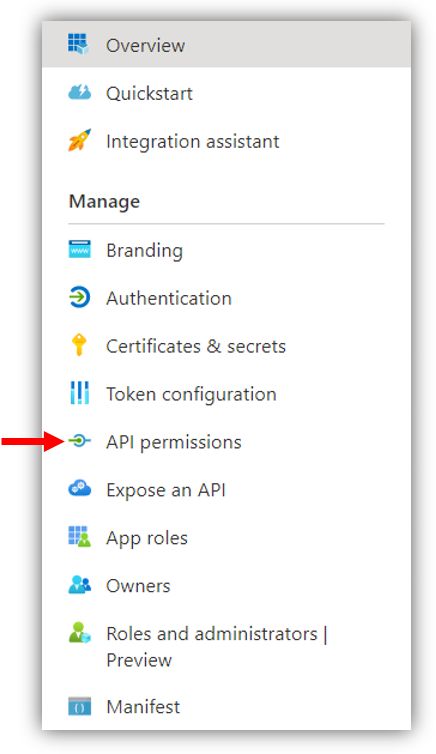
To do so, click on API Permissions from the left-hand menu:
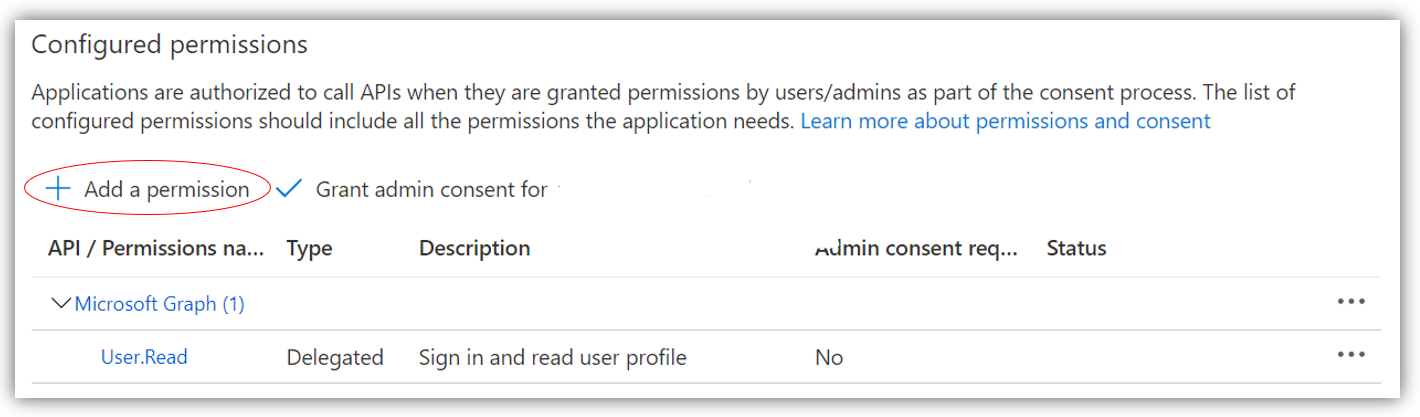
You will now see a screen resembling below. Click Add a Permission:
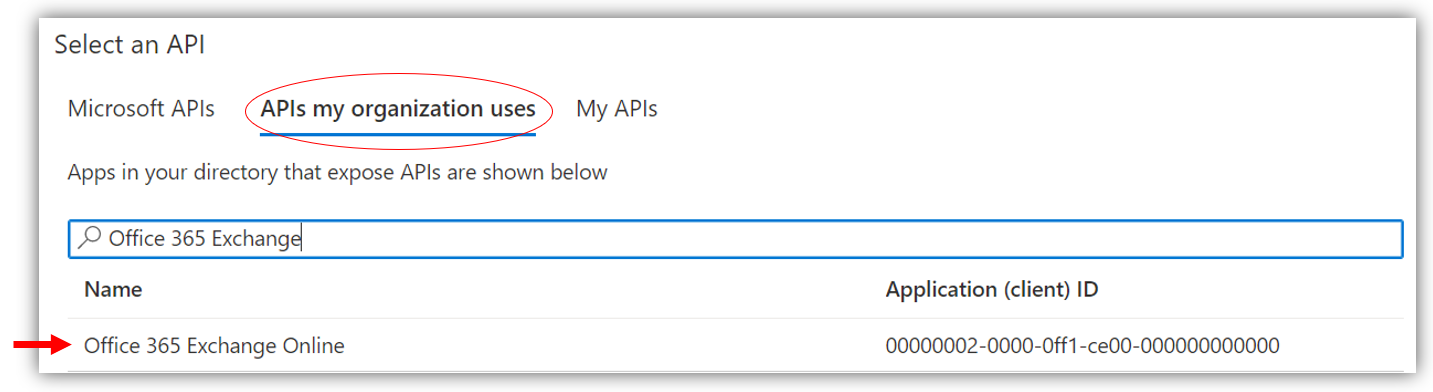
In the window that opens up, click on the tab APIs my Organisation Uses, and start typing 'Office 365 Exchange Online' in the search bar:
Once this appears below the search bar, click on it.
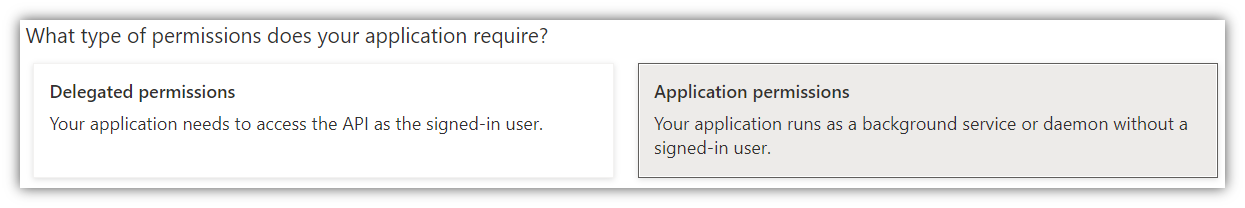
In the new window that opens, select the Application Permissions option underneath What type of permissions does your application require?:
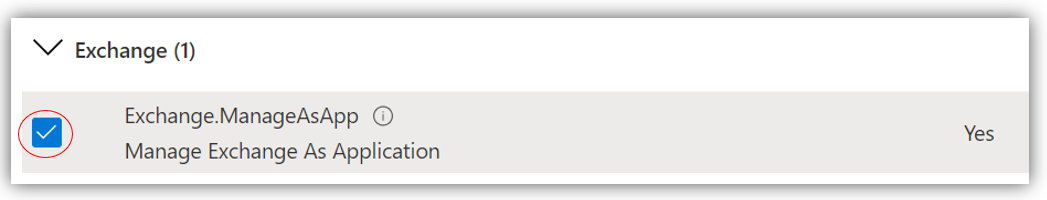
Then, scroll down until you find Exchange. Click on the expand button, and then tick the 'Exchange.ManageAsApp' option.
Now you can click Add Permissions to assign this permission to your application.
STEP 7: Grant Consent
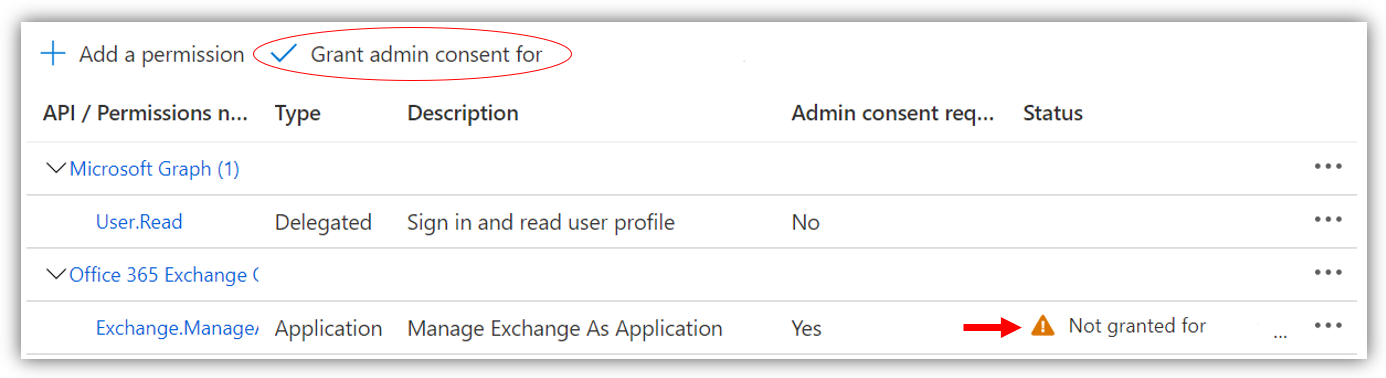
You should now see this permission listed under your Configured Permissions.
For now, there will be an orange warning icon in the Status column, indicating that you have not granted consent for this permission.
To consent, click the Grant admin consent for <name of your organisation> option.
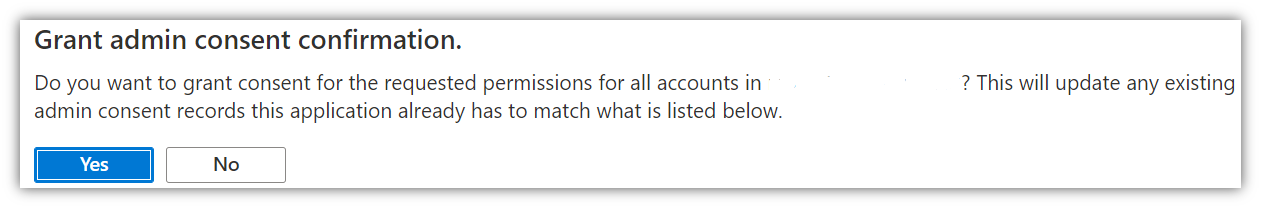
This will prompt you to grant admin consent confirmation. Click Yes to consent.
The previous orange warning icon in the Status column will now update to a green tick to reflect this. 
STEP 8: Assign HighGround.io - Defender for Office 365 to the role of Exchange Administrator
You now need to return to your Active Directory.
To do so, click on Microsoft Azure near the top-left of the screen: 
Then click on Azure Active Directory:
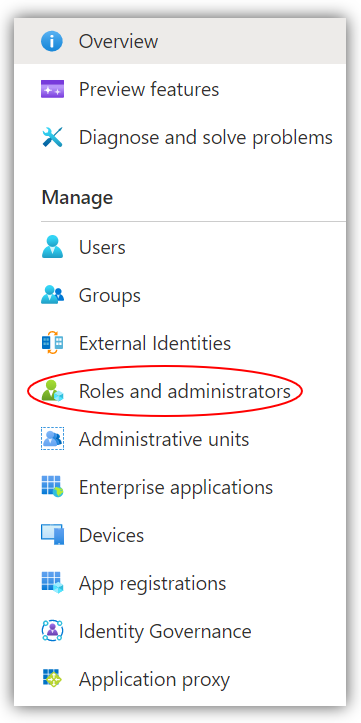
Once in the Active Directory, look to the main left-hand menu, and click on Roles and Administrators:
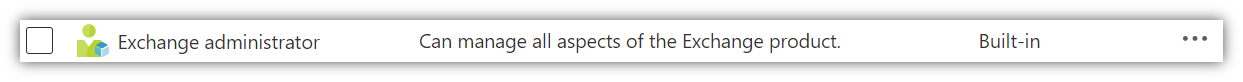
You should now see a list of Administrative roles. Scroll down this list until you see Exchange Administrator and click it.
Once you're inside the role, click Add assignments:
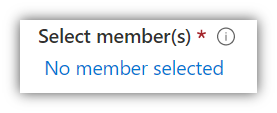
At the bottom of the Add assignments window you will see the option to Select member(s):
Click on No member selected, and begin typing 'HighGround.io - Defender for Office 365' into the search bar that appears. Once you see the HighGround.io App registration object that you created, click on it:
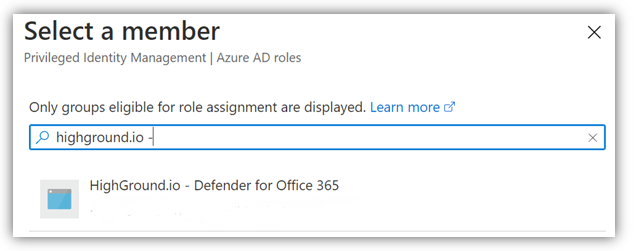
Now click Select.
And then Next:
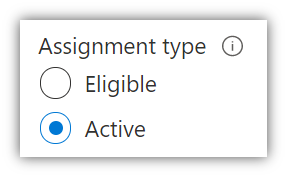
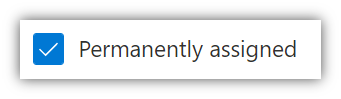
In the following window;
- Ensure that Assignment type is set to Active:
- Ensure the assignment is Permanently assigned:
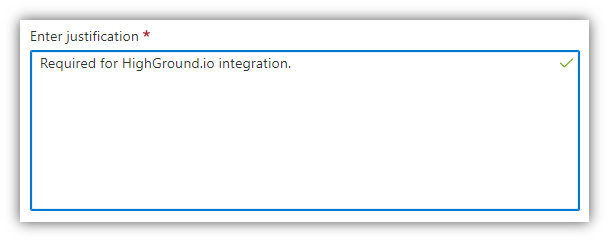
- Enter a short justification, such as the example below:
Leave the other settings at default.
Now click Assign to complete the process of assigning HighGround.io to the role of Exchange Administrator. 
STEP 9: Integrate Microsoft Defender for Office 365 to HighGround:
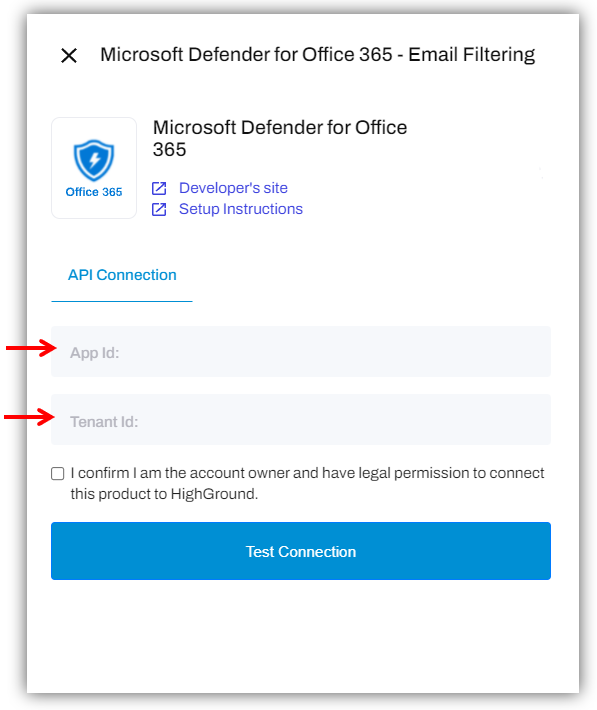
You can now use the Application (client) ID and Tenant ID retrieved in earlier steps to integrate the tool to your HighGround account.
To do so, you will need to go to the Integrations area of your HighGround account, and find the Microsoft Defender for Office 365 tool under the Email Filtering technology. Clicking on 'Connect Tool' will open a window for you to enter your integration details:
What happens next?
Continue with the integration setup (as pictured in the integration connection window above) to complete the process of connecting your Microsoft Defender for Office 365 tool to HighGround.
Note: that it may take up to 2 minutes to test the connection, so please do not navigate away from the window until this test has completed.
If you are unsure of how to complete the integration, you can look at our guide on How to Integrate a tool with your HighGround account.